Integrated Course: Side-Channel Analysis of Software
| Lecturer: | Dr. Artem Starostin |
| Form: | Integrated course (IV4) - 6CP |
| Language: | English |
| Place and time: | S2|02 C120, Mondays 18:05-19:45 and Wednesdays 9:50-11:30, starting from 14.10.15 |
| Exams: | Mid-term: 18.11.15 at 9:50 in S101/A04, Final: 10.02.16 at 9:50 in S101/A04 |
| Registration: | in TUCaN (course id 20-00-0927-iv) |
| Max. participants: | 80 |
Slides and exercise are available in Moodle.
Exam inspection
- The final exam inspection will take place on June 30, 10:00-11:00 in S202/E302. Please do not forget to bring your student's card and a photo ID (for instance your passport).
Exams
- Final exam will take place on 10. February 2016 starting from 9:50 in S101/A04. Please do not forget to bring your student's card and a photo ID (for instance your passport).
- Mid-term exam will take place on 18. November 2015 starting from 9:50 in S101/A04. Please do not forget to bring your student's card and a photo ID (for instance your passport).
Content
In this course we will study methods for detection, exploitation, assessment and mitigation of side channels in software. Covered topics will include:
- elements of information theory and program analysis,
- detection of side-channel vulnerabilities by program analysis,
- design, construction, and implementation of side-channel attacks,
- timing attacks, micro-architectural attacks, power attacks,
- information-theoretic modeling of side channels and side-channel attacks,
- quantitative assessment of side channels,
- design and evaluation of countermeasures against side channels.
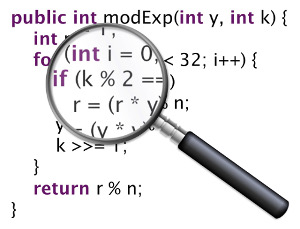
Side channels are unintended communication channels that transmit information during the execution of programs. Running time, power consumption, electromagnetic radiation, cache behavior, and other characteristics can cause side channels. Side channels may be correlated with secrets processed by programs e.g., private cryptographic keys, and this makes side channels a serious security concern. By exploiting the correlation between the information transmitted through a side channel and the secrets, a hacker can recover the secrets. This is known as a side-channel attack.
Due to improvements in security protection mechanisms, traditional security vulnerabilities, like programming bugs, are getting harder to exploit. That is why, side-channel vulnerabilities are becoming now more and more attractive to hackers. During the last two decades, side-channel attacks have been successfully demonstrated on many cryptographic algorithms (e.g., RSA, AES, DES), protocols (e.g., SSL, TLS, SSH), web applications, operating systems, mobile devices, and the cloud.
Side-channel analysis is the area of computer security that studies detection and assessment of side-channel vulnerabilities, construction of side-channel attacks, and design of proper countermeasures.
This lecture covers important topics which are part of the current research in the collaborative research center CROSSING.
Learning Objective
After successfully finishing the course you will be able to
- differentiate and explain types of side-channel vulnerabilities in software,
- identify side-channel vulnerabilities in software's program code,
- design program analyses for automatic detection of side-channel vulnerabilities,
- differentiate and explain types of side-channel attacks,
- design and implement side-channel attacks against software,
- model side channels and side-channel attacks using elements of information theory,
- derive information-theoretic bounds for side-channel leakage,
- empirically evaluate the seriousness of side channels,
- differentiate and explain countermeasures against side channels,
- secure programs against side-channel attacks by program transformation,
- argue about the effectiveness and efficiency of countermeasures against side channels,
- navigate in the security-performance trade-off in the context of side-channel mitigation.
Prerequisites
Knowledge of computer science equivalent to the first four semesters in the Computer Science Bachelor program, in particular basic knowledge of cryptography and semantics of programming languages.
Literature
- C. K. Koc, editor. Cryptographic Engineering. Springer, 2009
- C. Rebeiro, D. Mukhopadhyay, and S. Bhattacharya. Timing Channels in Cryptography: A Micro-Architectural Perspective. Springer, 2015
- V. D. Gligor. A Guide to Understanding Covert Channel Analysis of Trusted Systems (Light Pink Book). National Computer Security Center, 1993
- T. M. Cover and J. A. Thomas. Elements of Information Theory, Second Edition. Wiley, 2006
- L. Cardelli. Type systems. In Allen B. Tucker, editor, The Computer Science Handbook, Second Edition, pages 2313-2344. CRC Press, 2005
- Research articles on relevant topics.
About Lecturer
 |
Dr. Artem Starostin is a postdoctoral researcher at MAIS, TU Darmstadt. He has a PhD and MSc in Computer Science from Saarland University (Germany) and a Diploma in Software Engineering from Pacific National University (Russia). His research interests are security and software engineering, in particular side-channel analysis and mitigation, information-flow control, and program analysis. He is a member of IEEE and ACM. You can meet him during his office hour on Tuesdays 17:00-17:45 in office E319. |
Last modified on 28 June 2016.