Cassandra: A Security-Certifying App Store for Android
Apps running on Android smartphones have access to various private information of their users, e.g., contacts, appointments, and the GPS location. To protect such information, the Android operating system provides a mechanism for restricting access to it: the Android permission system. An app may only access a protected source of private information if it was granted the appropriate permission at the time of the app's installation. However, the user has no control on how private information is propagated by an app after it has been accessed legitimately. In fact, it has been observed that many apps abuse entrusted information by leaking it, e.g., to the Internet.
Cassandra aims at increasing the transparency of how apps use private information and, thus, supporting users in protecting their privacy. The primary goal of Cassandra is that no private data or other secret information is leaked by running an app.
Overview of the Tool
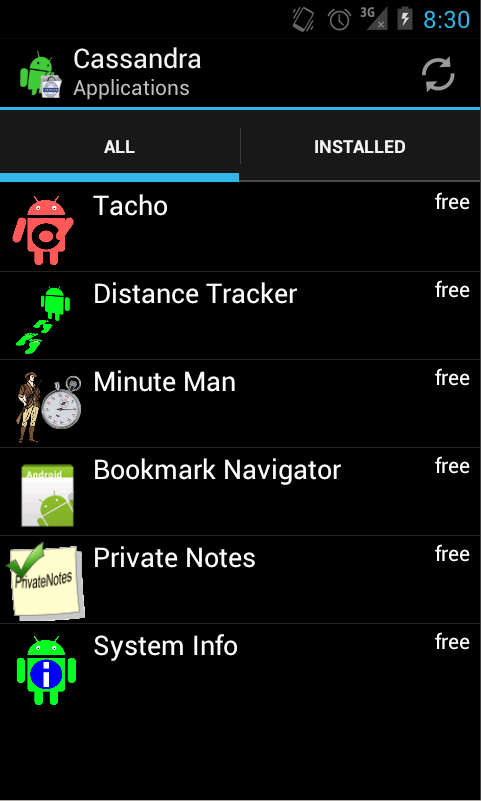
From a user's perspective, Cassandra resembles conventional app stores with respect to browsing and installing apps. In addition, Cassandra offers an interface for specifying security policies and for checking that apps adhere to these policies prior to installation.
Cassandra's architecture follows the client-server paradigm. The client of Cassandra is an Android app that provides an interface for browsing apps, for specifying security policies, and for viewing analysis results. The server is implemented in Java and PHP and provides its clients with apps to install, templates for specifying security policies, and a service for conducting the information-flow analysis.
 |
 |
 |
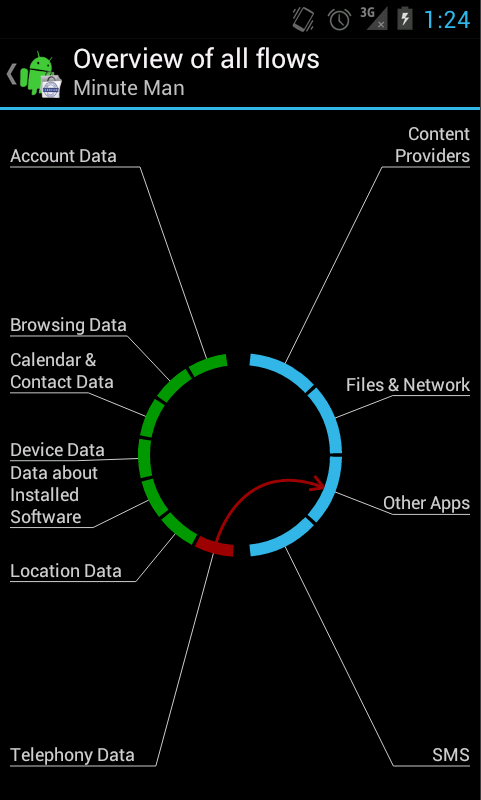 |
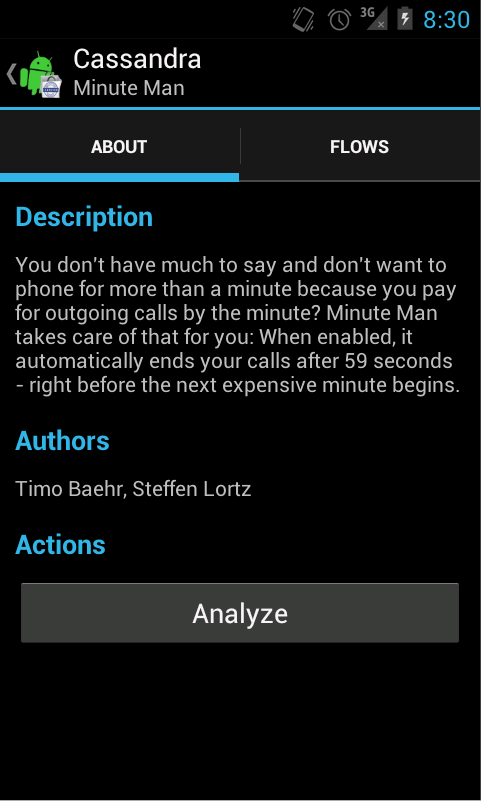
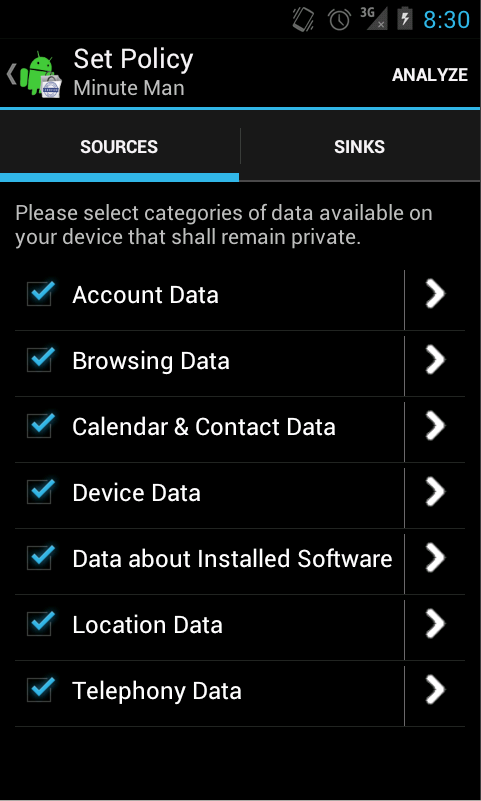
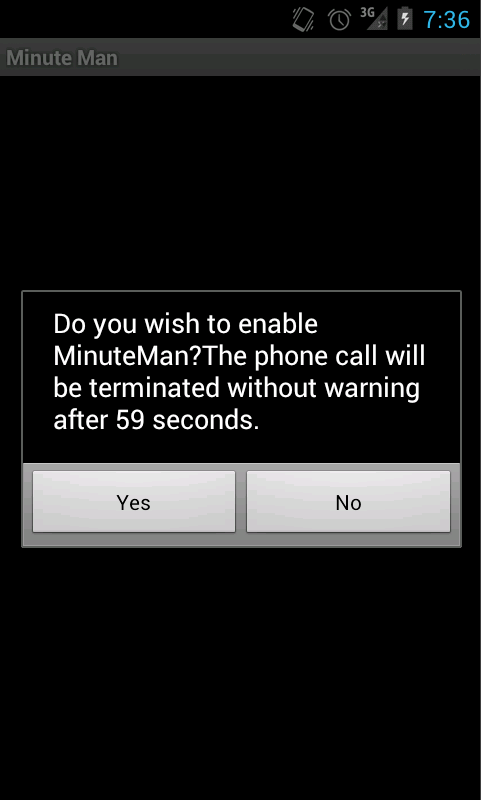
The screenshots show a part of the user interface of Cassandra's client app. From left to right, they show the app browser, the app viewer, the policy editor, and the reporter, respectively. To conduct a security analysis with Cassandra, the user first selects an app in the app browser. Second, he clicks the button "Analyze" below the app's description. Third, the user chooses sources of private information, and untrusted information sinks in the policy editor and confirms the selection by clicking "Analyze" again. After a few seconds, the user either gets a notification that the app respects his security requirements or he gets an overview of found information leaks in the app. Finally, the user can take an informed decision on whether to install the analyzed app or not. The video below shows the application of Cassandra at the example of the app "Minute Man", which reveals a leak of private information in the app.
Further details about the Architecture of Cassandra and its implementation are provided in [LMSBSW14].
Security Analysis
The security analysis of Cassandra automatically checks that no information obtained from a selected private source of information is leaked to a selected untrusted sink by running the analyzed app. The analysis implements a type-based information-flow analysis for Dalvik bytecode. This information-flow analysis has been proven to soundly enforce a noninterference-like, declarative security property. The definition of the security type system, the security property, and the soundness proof are given in [LMSW2014].
At this point in time, the sound security analysis of Cassandra supports 211 out of 218 Dalvik bytecode instructions. This is already sufficient for analyzing apps with meaningful functionality as those available in the Cassandra Demo below. The work to further improve the practical applicability of Cassandra's security analysis is in progress.
Demo
A demo of the Cassandra app store is available. It comprises an app store with selected apps, and a client app to access this store, which can be downloaded here. If you have trouble with running the demo or encounter bugs or other problems, please contact Alexandra Weber.
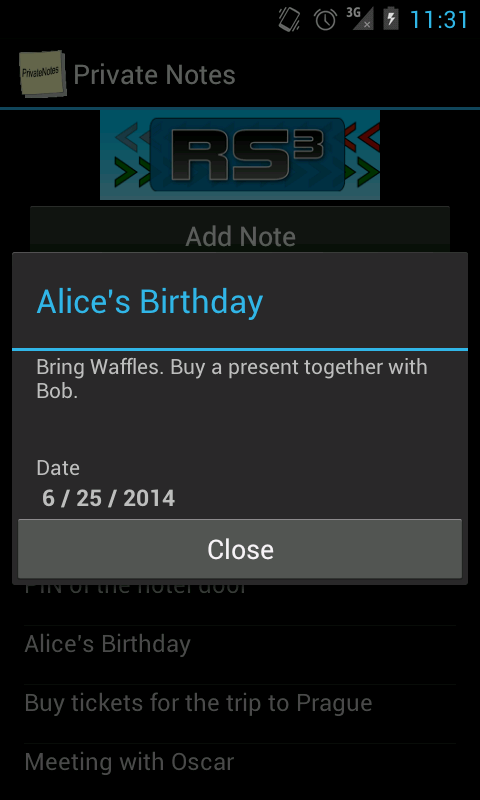
The app store offers three self-written apps that can be analyzed and installed: Distance Tracker, Minute Man, and Private Notes. A short description of the apps as well as an overview of their potential information leaks is provided in the following.
| Distance Tracker | Minute Man | Private Notes |
 |
 |
|
| Functionality: When started, the Distance Tracker measures the traveled distance as well as the speed of the mobile device. Besides this information, the app displays a link to the website of the app provider. | Functionality: When activated, Minute Man runs as a background service and offers the user to terminate outgoing phone calls within 59 seconds to save the money for the second minute. | Functionality: Private Notes allows its user to take and view notes. The notes are stored in the private persistent memory of the app. The app displays an advertisement banner that it loads from the Internet. |
| Leaks: The app leaks the recorded location information to the Internet when the link to the website is clicked. The location information is encoded into the URL that is opened with the web-browser. | Leaks: The app leaks the called phone number to a URL that is opened in the web- browser immediately after the app has terminated a call. | Leaks: The app does not leak sensitive information to any potentially untrusted information sink. |
Source Code
The source code of Cassandra is available under the MIT license and can be downloaded here.
Publications
- Tobias Hamann, Mihai Herda, Heiko Mantel, Martin Mohr, David Schneider and Markus Tasch. A Uniform Information-Flow-Security Benchmark Suite for Source Code and Bytecode. In Proceedings of the 23nd Nordic Conference on Secure IT Systems (NordSec), pages 437-453, 2018.
[ BibTeX entry | PDF ] - Steven Arzt, Alexandre Bartel, Richard Gay, Steffen Lortz, Enrico Lovat, Heiko Mantel, Martin Mohr, Benedikt Nordhoff, Matthias Perner, Siegfried Rasthofer, David Schneider, Gregor Snelting, Artem Starostin and Alexandra Weber. Software Security for Mobile Devices. Poster at the 25th USENIX Security Symposium, 2016.
[ BibTeX entry ] - Steven Arzt, Alexandre Bartel, Richard Gay, Steffen Lortz, Enrico Lovat, Heiko Mantel, Martin Mohr, Benedikt Nordhoff, Matthias Perner, Siegfried Rasthofer, David Schneider, Gregor Snelting, Artem Starostin and Alexandra Weber. Software Security for Mobile Devices. Poster at the 36th IEEE Symposium on Security and Privacy (S&P), 2015.
[ BibTeX entry | Abstract ] - Steffen Lortz, Heiko Mantel, David Schneider, Artem Starostin, Timo Bähr and Alexandra Weber. Certifying the Security of Android Applications with Cassandra. Short Talk at the 36th IEEE Symposium on Security and Privacy (S&P), 2015.
[ BibTeX entry | Abstract ] - Sarah Ereth, Steffen Lortz and Matthias Perner. Confidentiality for Android Apps: Specification and Verification. In it - Information Technology, 56(6), pages 288-293, 2014.
[ BibTeX entry ] - Steffen Lortz, Heiko Mantel, Artem Starostin and Alexandra Weber. A Sound Information-Flow Analysis for Cassandra. TU Darmstadt, Technical Report TUD-CS-2014-0064, 2014.
[ BibTeX entry | PDF ] - Steffen Lortz, Heiko Mantel, Artem Starostin, Timo Bähr and David Schneider. Cassandra: Towards a Certifying App Store. TU Darmstadt, Technical Report TUD-CS-2014-0117, 2014.
[ BibTeX entry | PDF ] - Steffen Lortz, Heiko Mantel, Artem Starostin, Timo Bähr, David Schneider and Alexandra Weber. Cassandra: Towards a Certifying App Store for Android. In Proceedings of the 4th ACM CCS Workshop on Security and Privacy in Smartphones and Mobile Devices (SPSM), pages 93-104. ACM, 2014.
[ BibTeX entry | PDF ] - Jan Erik Keller. Der typbasierte Nachweis von Noninterference für Dalvik-Programme mit Ausnahmebehandlung. Master Thesis, TU Darmstadt, 2014.
[ BibTeX entry ] - David Schneider. An Object-Sensitive Type-Based Information-Flow Analysis for Android Applications. Master Thesis, TU Darmstadt, 2014.
[ BibTeX entry ] - Pascal Wittmann. Confidentiality for Multithreaded Dalvik Programs by SIFUM Security. Bachelor Thesis, TU Darmstadt, 2013.
[ BibTeX entry ] - Christopher Mann and Artem Starostin. A Framework for Static Detection of Privacy Leaks in Android Applications. In Proceedings of the 27th Symposium on Applied Computing (SAC), Computer Security Track, pages 1457-1462. ACM, 2012.
[ BibTeX entry | PDF ] - Simon Reinhardt. Implementation and Evaluation of a Module for Type-based Information-Flow Analysis of Multi-threaded Programs on Android. Bachelor Thesis, TU Darmstadt, 2012.
[ BibTeX entry ] - Alexandra Weber. A Formal Model, a Noninterference Condition, and a Sound Type System for a Certifying Application Store. Bachelor Thesis, TU Darmstadt, 2012.
[ BibTeX entry ] - Christopher Mann. A Static Framework for Privacy Analysis of Android Applications. Bachelor Thesis, TU Darmstadt, 2011.
[ BibTeX entry ]